Microsoft releases PowerShell script to fix Windows 10/11 WinRE BitLocker bypass vulnerability
Microsoft has released dedicated PowerShell scripts to enterprise IT administrators this week for the purpose of fixing the CVE-2022-41099 vulnerability.
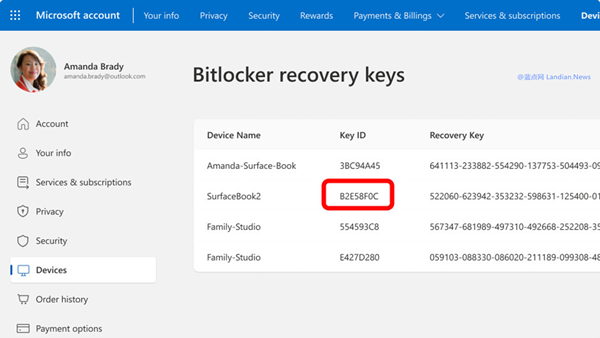
The vulnerability was first discovered on November 8, 2022. Attackers can exploit the vulnerability to bypass BitLocker disk encryption when they have physical access to a PC.
This poses a security risk for enterprises as attackers can bypass encryption policies and gain access to files stored on devices. Fortunately, this feature cannot be exploited remotely.
Microsoft had previously released security updates to fix the vulnerability. The newly released scripts are intended for devices that still cannot install these security updates.
▲Image from @BP
This security update refers to the PowerShell scripts that Microsoft has just released. Two versions of these scripts are available for enterprise IT administrators to use as needed.
The recommended script is PatchWinREScript_2004plus.ps1, which supports Windows 10 Version 2004 and above. This script is more robust but only supports limited system versions. When using this script, the system will automatically install the latest dynamic system update and update WinRE images.
PatchWinREScript_General.ps1 supports all versions of Windows 10/11 including older ones but its security logic is not as good as that of the previous script.
If an enterprise still cannot install updates, there is another way: enabling TPM+PIN protection so that hackers cannot decrypt data without PINs.
All these scripts require internet connection during execution. To avoid any potential issues, it's best practice to backup data or create recovery images with third-party software before running them.
When executing these scripts, WinRE image files will be automatically installed in current version systems instead of new ones.
Then through Safe OS provided by System Update Directory (SUD), online updating WinRE image will take place followed by unloading images.
BitLocker TPM protection program will then reconfigure WinRE image for BitLocker service again; at this point updated new images are used.
For information about KB5025175 update content and script download address please click here; For information about CVE-2022-41099 vulnerabilities please click here.